Computer Networks test questions for interview, exams, entrance
(1) We have two hosts A and B that are using sliding window protocol for flow control, and to transfer data from A to B full duplex link is used. The send window size and receive window size is 5 packets each. Data packets that are sent only from A to B are all 1000byte long and the transmission time for such a packet is 50µs. Acknowledgement packets that are sent only from B to A are very small and it requires negligible transmission time. In this communication the maximum achievable throughput, if the propagation delay over the link is 200µs, is(A) 9.12 x 10
6 bps
(B) 10.09 x 10
6 bps
(C) 12.33 x 10
6 bps
(D) 11.11 x 10
6 bps
View Answer / Hide Answer(2) The different activities pertaining to email are:a. Send an email from a mail client to mail server.
b. Download an email from mailbox server to a mail client.
c. Checking email in a web browser.
In each activity given above, the application level protocol used, is(A) a: SMTP, b: POP, c: HTTP
(B) a: SMTP, b: HTTP, c: POP
(C) a: POP, b: SMTP, c: HTTP
(D) a: SMTP, b: IMAP, c: POP
View Answer / Hide AnswerANSWER: a: SMTP, b: POP, c: HTTP
(A) IP packets from the same source to the same destination can take different routes in the network
(B) If the packet is unable to reach its destinations within a given number of hops, IP ensures that a packet is discarded
(C) A computer can have multiple IP address
(D) All of the above
View Answer / Hide AnswerANSWER: A computer can have multiple IP address
(A) 255.255.255.224
(B) 255.255.255.0
(C) 255.255.255.128
(D) 255.255.255.192
View Answer / Hide Answer For questions 5 and 6 refer to the data given below:
Let A, B and C be the three IP networks and Ha, Hb and Hc be the hosts of network A, network B and network c respectively. Message containing 180byte of application data is send by host Ha to host Hc through an intermediate network B. The TCP layer prefixes a 20byte header to the message. In each network, the maximum packet size including 20byte IP header is A: 1000byte, B: 100byte, C: 1000byte. The network A is connected to network B through a 1Mbps link and network B is connected to network C through a 512kbps link, where bps stands for bits per second.
(5) Consider the packets are correctly delivered. In the best case, how many bytes including headers are delivered to the IP layer at the destination, for one application message? Consider only data packets.(A) 200
(B) 220
(C) 240
(D) 260
View Answer / Hide Answer(6) Neglecting errors, acknowledgements and other overheads, the rate at which application data is transferred to host Hc, is(A) 150.8kbps
(B) 245.6kbps
(C) 400.9kbps
(D) 354.5kbps
View Answer / Hide Answer(7) For real time multimedia, file transfer, DNS and email, the transport layer protocols used are respectively(A) TCP, UDP, TCP and UDP
(B) UDP, UDP, TCP and TCP
(C) UDP, TCP, UDP and TCP
(D) TCP, TCP, UDP and UDP
View Answer / Hide AnswerANSWER: UDP, TCP, UDP and TCP
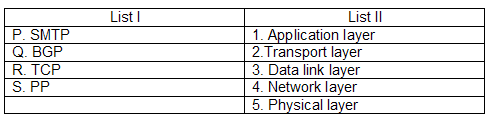
(A) P – 1, Q – 4, R – 2, S - 3
(B) P – 4, Q – 3, R – 2, S - 1
(C) P – 2, Q – 1, R – 4, S - 3
(D) P – 4, Q – 3, R – 1, S - 2
View Answer / Hide AnswerANSWER: P – 1, Q – 4, R – 2, S - 3
(A) It cannot block all ICMP traffic
(B) It cannot block entire HTTP traffic during 9:00pm and 5:00am
(C) It cannot block TCP traffic from a specific user on a multi-user system during 9:00pm and 5:00am
(D) It cannot stop incoming traffic from a specific IP address but allow outgoing traffic to the same address
View Answer / Hide AnswerANSWER: It cannot block TCP traffic from a specific user on a multi-user system during 9:00pm and 5:00am
(A) Network layer – 6 times and data link layer – 4 times
(B) Network layer – 4 times and data link layer – 2 times
(C) Network layer – 4 times and data link layer – 6 times
(D) Network layer – 2 times and data link layer – 3 times
View Answer / Hide AnswerANSWER: Network layer – 4 times and data link layer – 6 times
(A) Datagram
(B) Message
(C) Frame
(D) Segment
View Answer / Hide Answer(12) In the Ipv4 addressing format, how many networks are allowed under class C addresses?(A) 2
21 (B) 2
16 (C) 2
24(D) 2
7View Answer / Hide Answer(13) The transport layer protocols that is used to support electronic mail is(A) TCP
(B) SMTP
(C) UDP
(D) IP
View Answer / Hide Answer(14) We have an Ipv4 datagram with following specifications: M bit = 0,
The value is the of HLEN = 10,
The value of total length = 400,
The fragment offset value = 300,
What is the position of the datagram, the sequence numbers of the first and last bytes of the payload respectively?(A) First fragment, 2400 and 2759
(B) Middle fragment, 300 and 689
(C) Last fragment, 2400 and 2789
(D) Last fragment, 2400 and 2759
View Answer / Hide AnswerANSWER: Last fragment, 2400 and 2759
(A) 50bytes
(B) 100bytes
(C) 200bytes
(D) None of the above
View Answer / Hide AnswerANSWER: None of the above
(A) 1km
(B) 2km
(C) 5km
(D) 10km
View Answer / Hide Answer(17) The pair of IP addresses that could belong to a network whose subnet mask is 255.255.31.0 is(A) 10.35.28.2 and 10.35.29.4
(B) 172.57.88.62 and 172.56.87.233
(C) 128.8.129.43 and 128.8.161.55
(D) 191.203.31.87 and 191.243.31.88
View Answer / Hide AnswerANSWER: 128.8.129.43 and 128.8.161.55
(A) 512
(B) 440
(C) 100
(D) 350
View Answer / Hide Answer(19) The table given below is the routing table of a router: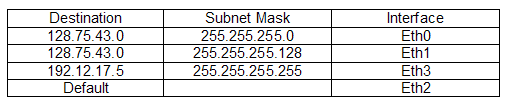
The interface where the router forward packets addressed to destinations 1 28.75.43.16 and 192.12.17.10 respectively is
(A) Eth0 and Eth2
(B) Eth0 and Eth3
(C) Eth1 and Eth3
(D) Eth1 and Eth2
View Answer / Hide Answer(20) A message that consists of 9 packets is to be send by station A to station B, using sliding window (window size 3) and go-back-n error control strategy. All packets are ready and immediately available for transmission. The number of packets A will transmit for sending the message to B, if every 5th packet that is transmitted by A gets lost (but no acts from B ever
gets lost), is(A) 20
(B) 9
(C) 15
(D) 12
View Answer / Hide Answer(21) On an Ethernet only two stations, station A and station B are present and each station has a steady queue of frames to send. In an attempt to transmit a frame both A and B collide and A wins the first backoff race. At the end of this successful transmission by A, both A and B attempt to transmit and collide. What is the probability that A wins the second
backoff race is (A) 0.625
(B) 0.5
(C) 1.0
(D) 0.75
View Answer / Hide Answer(22) Consider a packet switching network where packets are routed from source to destination along a simple path having two intermediate nodes. What will be the optimum packet size if the message size is 24 byte and each packet contains a header of 3 byte? (A) 8
(B) 7
(C) 9
(D) 5
View Answer / Hide Answer(23) Let A and B be the two computers that are configured as follows: IP address of A = 203.197.2.53
Netmask of A = 255.255.128.0
IP address of B = 203.197.75.201
Netmask of B = 255.255.192.0
The statement that holds true is
(A) B assumes A on the same network but A assumes B on different network
(B) A assumes B on the same network but B assumes A on different network
(C) Both A and B assumes they are on the same network
(D) Both A and B assumes they are on the different network
View Answer / Hide AnswerANSWER: A assumes B on the same network but B assumes A on different network
(A) 11001001011
(B) 11001010
(C) 11001001000
(D) 110010010011
View Answer / Hide Answer(25) To transmit messages to station B, station A uses 32 byte packets and a sliding window protocol. The round trip delay between A and B is 80ms and the bottleneck bandwidth on the path between A and B is 128 kbps. The optimal size of the window, A should have is(A) 440
(B) 100
(C) 320
(D) 40
View Answer / Hide Answer(26) The address of a class B host is to be split into subnets with a 6-bit subnet number. The maximum number of subnets and the maximum number of hosts in each subnet is(A) 62 subnets and 440 hosts
(B) 62 subnets and 262142 hosts
(C) 62 subnets and 267812 hosts
(D) 62 subnets and 1022 hosts
View Answer / Hide AnswerANSWER: 62 subnets and 1022 hosts
(A) 1 - (1-p)
n-1(B) (1-p)
n-1(C) np (1-p)
n-1 (D) p (1-p)
n-1View Answer / Hide Answer(28) Consider a class B network on the Internet that has a subnet mask of 255.255.248.0. The maximum number of hosts per subnet is(A) 2047
(B) 2046
(C) 1023
(D) 1024
View Answer / Hide Answer(29) The token bucket, which is filled at a rate of 2Mbps, regulates a computer on a 10Mbps network. It is initially filled to capacity with 16Mbits. The maximum duration for which the computer can transmit at the full 10Mbps is(A) 5s
(B) 4s
(C) 3s
(D) 2s
View Answer / Hide Answer For questions 30 and 31 refer to the data given below:Consider a 10
6 bps duplex link between two hosts. Frames of 1000 bits are to be transmitted into this link to maximally pack them in transit (within the link). The propagation time
is 25 ms.
(30) Assuming no time gap between transmission of two frames, the minimum number of bits required to represent the sequence numbers distinctly is(A) 5
(B) 4
(C) 3
(D) 2
View Answer / Hide Answer(31) The size of the sender window is 21 where 1 is the number of bits identified in the earlier part and acknowledgements are always piggy backed. The sliding window protocol is used with this sender window. After sending 21 frames, the minimum time the sender will have to wait before starting transmission of the next frame is (Identify the closest
choice ignoring the frame processing time(A) 14ms
(B) 16ms
(C) 18ms
(D) 20ms
View Answer / Hide Answer(32) The transmission speed and the propagation speed in a token ring network is 107 bps and 200m/µs respectively. The 1-bit delay in this network is equivalent to(A) 5m of cable
(B) 20 m of cable
(C) 100 m of cable
(D) 500 m of cable
View Answer / Hide Answer(33) The size of the congestion window in the slow start phase of the TCP congestion algorithm(A) Decreases exponentially
(B) Increases exponentially
(C) Increases linearly
(D) Does not increase
View Answer / Hide AnswerANSWER: Increases exponentially
(A) (1 + x) is a factor of G (x)
(B) G (x) has an odd number of terms
(C) G (x) contains more than two terms
(D) It is not necessary to satisfy any condition
View Answer / Hide AnswerANSWER: (1 + x) is a factor of G (x)
(A) For fault tolerance
(B) For shortest path routing between LAN’s
(C) To minimize collisions
(D) To avoid loops in the routing paths
View Answer / Hide AnswerANSWER: To avoid loops in the routing paths
(A) 800
(B) 500
(C) 1000
(D) 440
View Answer / Hide Answer(37) In serial transmission why every byte of data is padded with a 0 in the beginning and one or two 1’s at the end of byte?(A) Because receiver recovers lost 0’s and 1’s from these padded bits
(B) Because padded bits are useful in parity computation
(C) To synchronize the receiver for byte reception
(D) None of the above
View Answer / Hide AnswerANSWER: To synchronize the receiver for byte reception
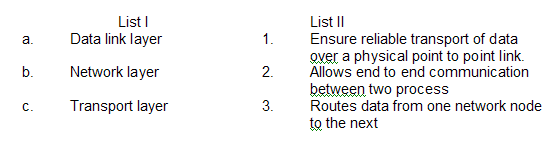
(A) a – 3, b – 2, c - 1
(B) a – 1, b – 3, c - 2
(C) a – 2, b – 3, c - 1
(D) a – 1, b – 2, c - 3
View Answer / Hide AnswerANSWER: a – 1, b – 3, c - 2
(A) End to end connectivity
(B) Recovery from packet losses
(C) Detection of duplicate packets
(D) Packet delivery in the correct order
View Answer / Hide AnswerANSWER: End to end connectivity
(A) A bridge builds up its routing table by inspecting incoming packets
(B) A router can connect between LAN and WAN
(C) Bridge uses IP address and routers uses MAC address
(D) Both bridge and router selectively forward data packets
View Answer / Hide AnswerANSWER: Bridge uses IP address and routers uses MAC address
(A) 255.255.64.0
(B) 255.255.0.0
(C) 255.255.1.28.0
(D) 255.255.255.0
View Answer / Hide Answer(42) In an IP datagram one of the header fields is time to live (TTL) field because(A) It can be used to prevent packet looping
(B) It can be used to optimize throughput
(C) It can be used to reduce delays
(D) It can be used to prioritize packets
View Answer / Hide AnswerANSWER: It can be used to prevent packet looping
(A) UDP but not TCP
(B) TCP and UDP
(C) TCP but not UDP
(D) Neither TCP nor UDP
View Answer / Hide Answer(44) The system calls that results in the sending of SYN packets is(A) Listen
(B) Socket
(C) Connect
(D) Bind
View Answer / Hide Answer(45) Why does the Internet protocol use time to live (TTL) field in the IP datagram header?(A) Limit the time for which a packet gets queued in intermediate routers
(B) Prevent packets from looping indefinitely
(C) Ensure packets reach destination within that time
(D) Discard packets that reach later than that time
View Answer / Hide AnswerANSWER: Discard packets that reach later than that time
(A) To find the MAC address corresponding to an IP address.
(B) To find an IP address corresponding to the MAC address
(C) To find the IP address from the DNS
(D) To find the IP address of the default gateway
View Answer / Hide AnswerANSWER: To find the MAC address corresponding to an IP address.
(A) Same as the baud rate
(B) Half of the baud rate
(C) Twice the baud rate
(D) None of the above
View Answer / Hide AnswerANSWER: Twice the baud rate
(A) 1500 byte
(B) 2
16 byte size of TCP header
(C) 2
16 byte
(D) Any size
View Answer / Hide AnswerANSWER: 216 byte size of TCP header
(A) SMTP
(B) HTTP
(C) DNS
(D) Telnet
View Answer / Hide Answer(50) The data is to be transmitted using the selective reject protocol with n bit frame sequence number. What is the maximum window size for this transmission?(A) 2
n-1 (B) 2
n-2(C) 2
n(D) 2
n -1
View Answer / Hide Answer