Operating System questions for Computer Science students.
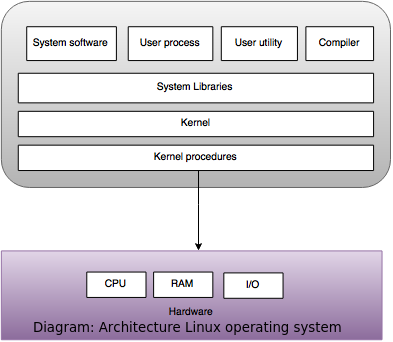
What is an operating system?
- An operating system is a collection of software programs which controls allocation and usage of various hardware resources in the system.
- It is the first program to be loaded in the computer and it runs in the memory till the system is shut down.
Some of the popular Operating Systems are:
DOS, Windows, Linux, solaris etc.
What is a compiler?
- A compiler is a program that takes a source code as an input and converts it into an object code.
- During the compilation process the source code goes through lexical analysis, parsing and intermediate code generation which is then optimized to give final output as an object code.
Explain Process.
- A process is a program that is running and under execution.
- On batch systems, it is called as a "job" while on time sharing systems, it is called as a "task".
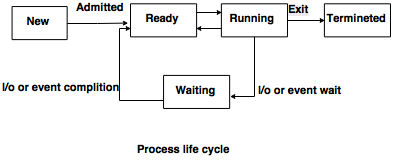
Explain the basic functions of process management.
Important functions of process management are:- Creation and deletion of system processes.
- Creation and deletion of users.
- CPU scheduling.
- Process communication and synchronization.
What do you know about a Pipe? When is it used?
- Pipe is an IPC (Inter process communication) mechanism used for one way communication between two processes which are related.
- A single process doesn't need to use pipe. It is used when two process wish to communicate one-way.
What are the various IPC( Inter Process Communication) mechanisms?
Various IPC mechanisms are:- Sockets.
- Pipes
- Shared memory
- Signals
- Message Queues
What are sockets?
- A socket is defined as endpoints for communication, a pair of sockets is used by the pair of processes.
- It is made of IP address chained with a port number.
- They use the client server architecture.
- Server waits for incoming client requests by responding to specified port.
- On reception of request, server accepts connection from client socket to complete the connection.
What is a semaphore?
- A semaphore is a hardware or a software tag variable whose value indicates the status of a common resource.
- Its purpose is to lock the common resource being used.
- A process which needs the resource will check the semaphore to determine the status of the resource followed by the decision for proceeding.
- In multitasking operating systems, the activities are synchronized by using the semaphore techniques.
What is the difference between a semaphore wait signal and a condition variable wait signal?
| Semaphore wait signal | Condition variable wait signal |
|---|
| Semaphore wait signal is not used in process monitoring. | Condition variable wait signal is only used in process monitoring. |
| The wait() function does not always blocks its caller. | The wait() function always blocks its caller. |
| The signal() function increments the semaphore counter and can release a process. | The signal() function is either release process or it is lost as if it never occurred. |
| If the signal() releases a process, the released process and the caller both continue the process. | On signal() releasing a process either the caller or the released process continues but not both at the same time. |
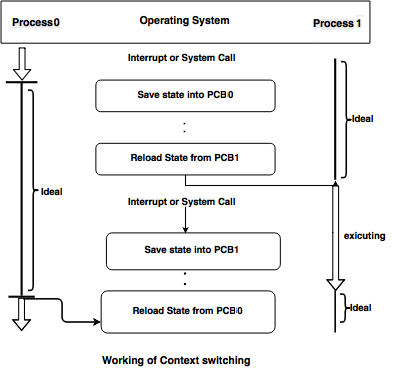
What is context switching?
- When Operating System saves the context of program that is currently running and restores the context of the next ready to run process, it is called as context switching.
- Context is associated with each process encompassing all the information describing the current execution state of the process.
- It is important for multitasking in operating system.
What are the advantages and disadvantages of circuit switching?
- The advantage of using circuit switching is that it ensures the availability of resources.
- That is it reserves the network resources required for a specific transfer prior to the transmission taking place.
- By doing so it ensures that no packet would be dropped and the required quality of service is met.
- The disadvantage of using circuit switching is that it requires a round trip message to setup a reservation.
- By doing so as it provisions the resources ahead of the transmission it might lead to the suboptimal use of resources.
What is scheduling?
- We can define scheduling as process handling manager.
- Scheduling allows more than one process to be loaded into the executable memory at a time and running process shares the CPU using time multiplexing.
- Scheduling decides which processes in the ready queue are to be allocated to the CPU for execution.
What are the different types of scheduling algorithms?
Preemptive algorithms:
In this type of scheduling a process maybe interrupted during execution and the CPU maybe allocated to another process.
Non-Preemptive algorithms:
In this type of scheduling once a CPU has been allocated to a process it would not release the CPU till a request for termination or switching to waiting state occurs.
Explain difference between Preemptive and Non-preemptive scheduling.
| Preemptive scheduling | Non-preemptive scheduling |
|---|
| Preemptive scheduling allows interruption of a process while it is executing and taking the CPU to another process. | Non preemptive scheduling ensures that a process keeps the CPU under control until it has completed execution. |
| Preemptive scheduling requires context switching more frequently. | Non-preemptive scheduling does not required context switching. |
| Preemptive scheduling is suited for real time systems. | Non-preemptive scheduling is not suited for real time systems. |
What is a deadlock?
- Deadlock is a condition where a group of two or more waiting process for the resources that are currently being used by other processes of the same group.
- In this situation every process is waiting for an event to be triggered by another process of the group.
- Since no thread can free up the resource a deadlock occurs and the application hangs.
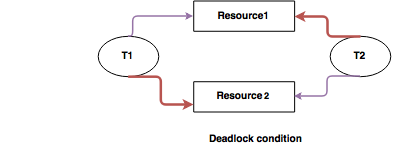
- In above diagram thread T1 has Lock on Resource 1 and waiting for Resource 2 to complete execution.
- Thread T2 has lock on Resource 2 and waiting for Resource 1 to complete execution.
What are the necessary conditions for deadlock to occur?
There are four necessary conditions that are required for a deadlock to occur:
Mutual Exclusion:
The resources available are not sharable. This implies that the resources used must be mutually exclusive.
Hold and Wait:
Any process requires some resources in order to be executed. In case of insufficient availability of resources a process can take the available resources, hold them and wait for more resources to architecture be available.
No Preemption:
The resources that a process has on hold can only be released by the process itself voluntarily. This resource cannot be preempted by the system.
Circular Waiting:
A special type of waiting in which one process is waiting for the resources held by a second process. The second process is in turn waiting for the resources held by the first process.
Is it possible to have a deadlock involving only one process? Explain.
- Deadlock with one process is not possible.
- Deadlock situation can arise only if the following four conditions hold simultaneously.
a) Mutual Exclusion.
b) Hold and Wait.
c) No Preemption.
d) Circular-wait.
- It is not possible to have circular wait with only one process, since there is no second process to form a circle with the first one.
Explain condition variable.
- Condition variables are synchronization objects which help threads to wait for particular conditions to occur.
- Without condition variable, the thread has to continuously check the condition.
- Condition variable allows the thread to sleep and wait for the condition variable to give it a signal.
List the functions constituting the OS's memory management.
- Memory allocation and de-allocation
- Integrity maintenance
- Swapping
- Virtual memory
Explain Main memory and Secondary memory storage.
a)Main memory:- Main memory is also known as random access memory (RAM).
- CPU can access Main memory directly.
- Data access from main memory is much faster than Secondary memory.
- Main memory is implemented in a semiconductor technology, called dynamic random-access memory (DRAM).
- Main memory is usually too small to store all needed programs.
- Main memory is a volatile storage device that loses its contents when power is turned off.
b)Secondary memory:- Magnetic disk is the most common secondary storage device.
- Secondary memory can store large amount of data and programs permanently.
- If a user wants to execute any program it should come from secondary memory to main memory because CPU can access main memory directly.
Differentiate between logical and physical address.
| Logical address | Physical address |
|---|
| Logical address are generated by user programs. | Physical address are actual address used for fetching and storing data in main memory when the process is under execution. |
| During process loading, Logical address are converted by the loader into physical address. | Physical memory is the only memory that is directly accessible to the CPU. |
Explain working of copying garbage collector and how can it be implemented using semispaces?
- Any object that is not copied in memory is garbage.
- Copying garbage collector basically goes through live objects and copying them into a specific region in the memory.
- This collector traces through all the live objects one by one.
- Entire process is performed in a single pass. Any object that is not copied in memory is garbage.
- The copying garbage collector can be implemented using semispaces by splitting the heap into two halves.
- Each half is a contiguous memory region.
- All the allocations are made from a single half of the heap only.
- When the specified heap is half , the collector is immediately invoked and it copies the live objects into the other half of the heap. In this way, the first half of the heap then only contains garbage and eventually is overwritten in the next pass.
Explain Belady's anomaly?
- The Belady's anomaly is a situation in which the number of page faults increases when additional physical memory is added to a system.
- This anomaly arises in some algorithms that implement virtual memory.
- An algorithm suffers from this problem when it cannot guarantee that a page will be kept when a small number of frames are available.
- An optimal algorithm would not suffer from this problem as it replaces the page not to be used for the longest time.
- The anomaly occurs when the page replacement algorithm will remove a page that will be needed in the immediate future.
- An optimal algorithm will not select such a page that will be required immediately.
- This anomaly is also stated to be unbounded.
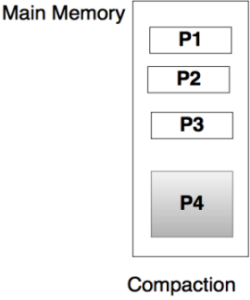
Explain compaction.
- During the process of loading and removal of process in and out of the memory, the free memory gets broken into smaller pieces.
- Compaction means movement of these pieces close to each other to form a larger chunk of memory which works as a resource to run larger processes.
- For example: In following diagram process P1, P2,P3 are put together in one large block P4.
Why is interrupt vector used in operating systems?
- Interrupt vector contains the addresses of the interrupt service routines for various devices.
- Here the interrupts can be indirectly called through the table with no intermediate routine needed.
- This leads to interrupt handling at a faster rate.
- Operating systems like MS DOS and UNIX are using the interrupt vector.
- faster speed.
What are the possible errors that may occur while an input file is opened?
- At the time of opening if the file is protected against access that file terminates abruptly.
- We need to create the output file if file already exists.
- If file with the same name exists, then it may be deleted or program may be aborted.
- In another case the system may ask the user to replace the existing file or abort the programs.
Describe system calls and its type.
- System calls work as a mediator between user program and service provided by operating system.
- In actual situation, functions that make up an API (Application program interface) typically invoke the actual system calls on the behalf of application programmer.
Types of System Call:
| Sr. No. | Types | Example |
|---|
| 1 | Process control | Create process, terminate process, end, allocate and free memory etc. |
| 2 | File manipulation | Create file, delete file, open file, close file, read, write. |
| 3 | Device manipulation | Request device, release device, read, write, reposition, get device attributes, set device attributes etc. |
| 4 | Information maintenance | Get or set process, file, or device attributes. |
| 5 | Communications | Send, receive messages, transfer status information. |
What is a Kernel?
- Kernel is the part of OS which handles all details of sharing resources and device handling.
- Its purpose is to handle the communication between software and hardware.
- Its services are used through system calls.
What are the main functions of a Kernel?
The main functions of a Kernel are:- Process management
- Device management
- Memory management
- Interrupt handling
- I/O communication
- File system management
What are the different types of Kernel?
The Two types of kernels are as follows:
a)Monolithic Kernels- In this all the system services were packaged into a single system module which lead to poor maintainability and huge size of kernel.
b)Micro kernels- It can follow the modular approach of architecture.
- Maintainability becomes easier with this model as only the concerned module is to be altered and loaded for every function.
- This model also keeps a tab on the ever growing code size of the kernel.
What is a command interpreter?
- Command interpreter is a program that interprets the command input through keyboard or command batch file.
- It helps the user to interact with the OS and trigger the required system programs or execute some user application.
Command interpreter can be referred as:- Control card interpreter
- Command line interpreter
- Console command processor
- Shell
What are read-write locks?
- Read-write locks provides simultaneous read access to many threads while the write access stays with one thread at a time.
- They are especially useful in protecting the data that is not frequently written but read simultaneously by many threads.
- They are slower than mutexes.
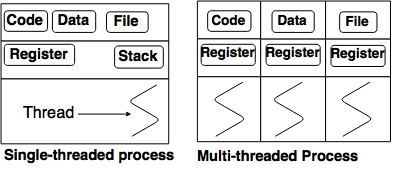
What is thread?
- It is an independent flow of control within a process.
- It consists of a context and a sequence of instructions for execution.
What are the advantages and disadvantages of threads?
a) Advantages:- No special communication mechanism is required.
- Readability and simplicity of program structure increases with threads.
- System becomes more efficient with less requirement of system resources.
b) Disadvantages- Threads can not be re-used as they exist within a single process.
- They corrupt the address space of their process.
- They need synchronization for concurrent read-write access to memory.
What is positioning time for a disk?
- It is also called as the random access time used by a disk to perform operations.
- It consists of time to move the disk arm to the desired cylinder called the seek time(seek time is the time taken by the head to move one cylinder to another).
- The Untitled Diagram.xml time required for the desired sector to rotate to the disk head is called rotational latency.
- Typical disks can transfer megabytes of data per second.
- Seek time and rotational latency is always in milliseconds.
What is EIDE (Enhanced integrated drive electronics)?
- It is an advanced version of IDE(integrated drive electronics).
- The input output devices are attached to the computer by a set of wires called the bus.
- The data transfer on a bus are carried out by electronic processes called controllers.
- The host controller sends messages to device controller and device controller performs the operations.
- These device controllers consist of built in cache so that data transfer occurs at.
What is role of DLM (distributed lock manager) in operating system?
- In cluster systems to avoid file sharing the distributed systems must provide the access control and file locking.
- This ensures that no conflicting operations occur in the system.
- Here the distributed file systems are not general purpose therefore it requires locking.
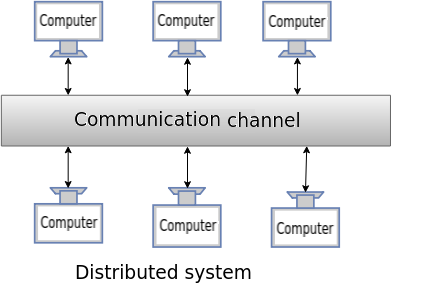
What are loosely coupled systems?
- Loosely Coupled systems are also known as distributed systems.
- It consist of a collection of processors that do not share memory or clock.
- The processors communicate through high speed buses or telephone lines.
- It can be a centralized system where the server responds to client requests.
- It can also be a peer to peer system.
Explain daemons in Unix.
- A demon is longtime running process that answers requests for services.
- The name of daemons usually end with 'd' at the end in Unix.
- For example: httpd, named, lpd.
Explain the layers of a Windows XP system.
1. Hardware abstraction layer:- A situation of operating system portability is created in this layer by hiding hardware differences from the operating systems upper layers.
- A virtual machine interface is provided by the hardware abstraction layer to be used by the kernel dispatcher and the device drivers.
2. Kernel layer:- The foundation provided in this layer is used by the executive functions and the user mode sub systems.
- Kernel would always remain in memory and cannot be preempted.
3. Executive layer:- Executive layer is responsible for providing services to be used by all subsystems.
- For example, object manager, process manager, i/o manager etc.